When was the last time you double checked to make sure your data is secure? What about the data you handle for your clients?
We recently told folks using Raven software they should change their passwords after we responded to the Heartbleed bug, which affected half the Internet. Very few people use only half the Internet, so security breaches impact almost everyone with an Internet connection.
New vulnerabilities pop up daily. Changing one setting can save you from a stressful week. For instance, Buffer’s GitHub account was hacked before it implemented 2-step authentication.
Having a long term strategy in place to protect your data and your clients’ data is crucial.
Data Security for You and Your Clients
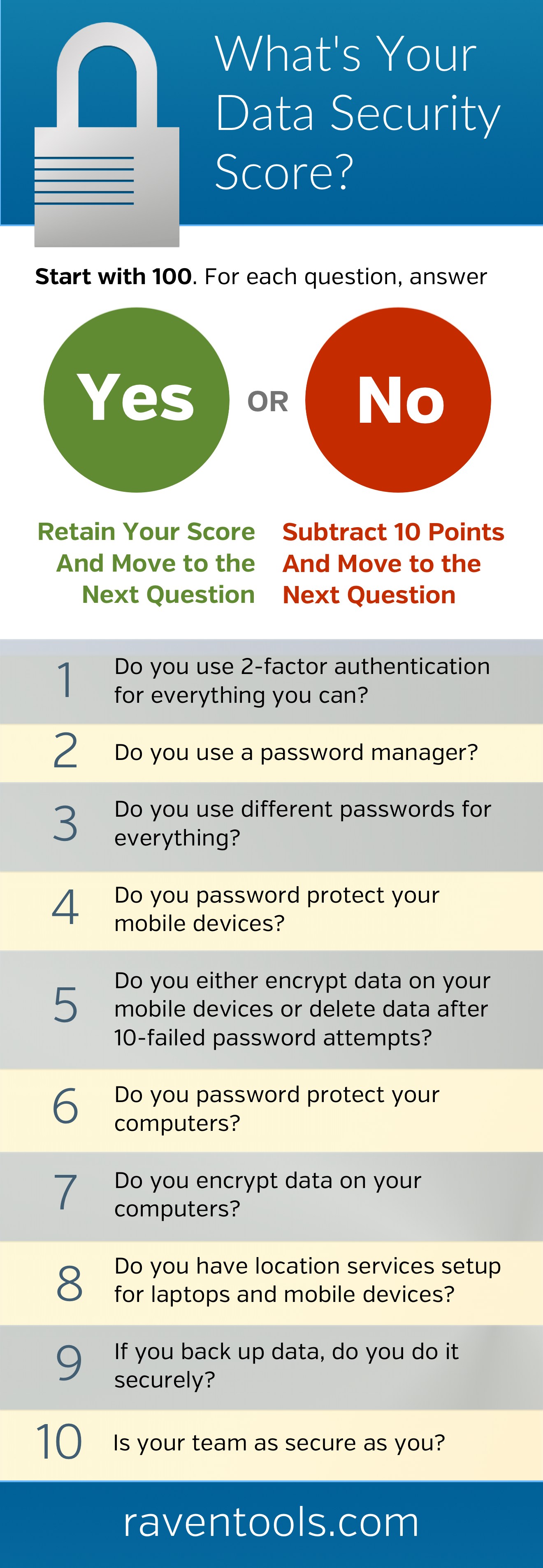
See how you score to determine how vulnerable you could be:
Use this list to make sure your data and your clients’ data is secure. Checking this important item off your list is low impact and high reward. Plus, you’ll have a great reason to reach out to clients.
1. Enable 2-Factor Authentication
Enable 2-factor authentication for everything you can. If you use Google, start by securing Gmail and Google Drive for any work and personal accounts. Loads of services support 2-factor authentication including WordPress, Facebook, Twitter, LinkedIn, Apple, Dropbox, LastPass, Evernote, Paypal, Amazon Web Services and GitHub.
2. Use a Password Manager
Use a password manager and maintain separate, strong passwords for all of your accounts. Use something like LastPass or 1Password. Be sure to use a unique, strong password for this account. Consider using a pass phrase and make sure you enable 2-factor authentication for your password manager.
3. Use Different Passwords for Everything
Using your password manager, create different strong passwords for all your accounts. Review the categories below and build a list to knock out. Remember to change all passwords for work and personal accounts.
Consider services for:
- Email (remember any accounts you setup for projects or social accounts)
- Code (domain name registrars, DNS software, hosting, file transfer apps, server software and code repositories)
- Banking
- Ad platforms
- Marketing software
- Blogs
- Social media accounts
- Team and communication apps
4. Password Protect Your Mobile Devices
Make sure you have a strong password protecting your mobile phones and tablets.
iOS: Settings > Passcode
Android: Settings > Security > Screen Lock


5. Encrypt Data on Your Mobile Devices
iOS: Settings > Passcode > Erase Data
Set your iOS device to delete all data after 10 consecutive failed password attempts. Pro Tip: If you have small kids, don’t let them play with your iPhone anymore.
Android: Settings > Security > Encrypt Phone
If you have Android devices, you can encrypt all your personal data.
6. Password Protect Your Computers
Don’t forget about those old laptops sitting in the intern’s room or the computer in the podcast corner.
Mac: Apple menu > System Preferences > Security & Privacy > General > Require Password
Windows: Control Panel > User Accounts > Add a user with a password
7. Encrypt Data on Your Computers
Mac: Apple menu > System Preferences > Security & Privacy > FileVault > Turn On FileVault
Windows 7 and 8: Search for “BitLocker” and follow steps to enable BitLocker Drive Encryption
Linux: Encrypt your home directory.
8. Set up Location Services
Setup location services for your phones, tablets and laptops.
Mac: Apple menu > System Preferences > iCloud > Find My Mac
iOS: Settings > iCloud > Find My iPhone/iPad
Windows/Linux: Download and set up Prey.
Android: Download and set up Lookout.
9. Use a Secure Backup Solution
If you are backing up data, make sure your second set of data is encrypted. Services like Backblaze or Mozy can do this behind the scenes for you.
10. Make Sure Your Team is as Secure as You
A network is as strong as the weakest link. Share this post with your team if you don’t already have a security checklist in place.
White Labeled and Branded Reports. Drag and Drop Editor. Automate your SEO, PPC, Social, Email, and Call Tracking Reporting.